Windows 11 finally arrived. Although many people were quite satisfied with the features that Windows 10 offered, this new operating system brings all kinds of improvements, with security and performance being the most important.
Windows 11 is currently available free of charge to anyone who has registered their Microsoft account as part of the Windows Insider testing program. However, this is not the only requirement to be able to install Windows 11 on a computer.

To be more specific, this is the official list of minimum requirements for Windows 11:
-
Processor: 1 gigahertz (GHz) or faster with two or more cores on a compatible 64-bit processor or system on a chip (SoC).
-
RAM: 4 gigabytes (GB) or greater.
-
Storage: 64 GB* or greater available storage is required to install Windows 11.
-
Additional storage space might be required to download updates and enable specific features.
-
Graphics card: Compatible with DirectX 12 or later, with a WDDM 2.0 driver.
-
System firmware: UEFI, Secure Boot capable.
-
TPM: Trusted Platform Module (TPM) version 2.0.
-
Display: High definition (720p) display, 9" or greater monitor, 8 bits per color channel.
In this article
Feature 1: TPM 2.0 and Secure Boot
It is important to note that most of the security options available today are software-based. This means that they do not provide specialized security protection against direct attacks on hardware. The TPM microcontrollers were designed to solve this problem.
TPM
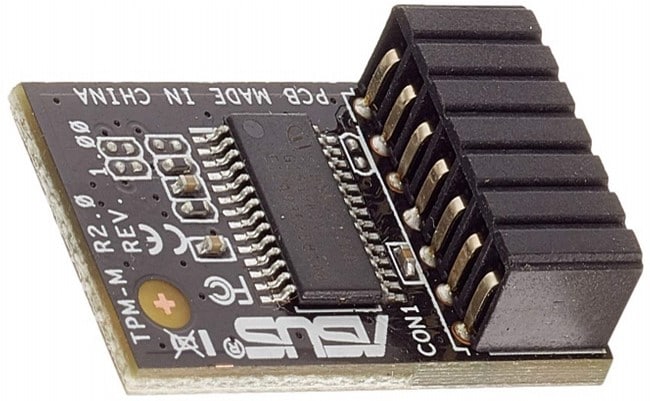
TPM (Trusted Platform Module) is a secure cryptoprocessor, these are specially designed to manage cryptography data and protect the integrity of system boot files.
TPM microcontrollers are not new. It is known that this technology has existed since 2004 and they have been used since mid-2006 in portable devices in order to prevent them from being attacked or modified since, due to their portable nature, they tend to be more physically exposed to attack. When a key or a certificate is generated for encrypted data, those keys and certificates are stored in the TPM.
TMP
TPM microcontrollers, together with operating system data management security protocols are responsible for creating a report of the configurations and current status, both software and hardware and generates an authenticity code with which a complex cryptographic algorithm is resolved.
In other words, the TPM microcontrollers are responsible for making unalterable reports of the current integrity status of the computer's software and hardware. This means that a TPM microcontroller is able to identify when hardware or software has been intentionally modified.
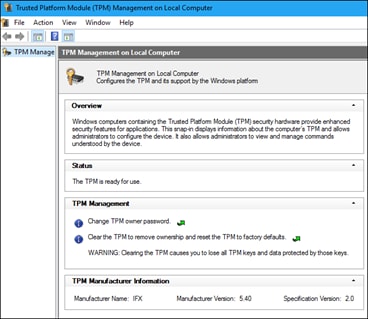
If you are currently using Windows 11 or if you are using Windows 10 and want to find out if your computer has a TPM microcontroller, you can press "Win + R" and type "tpm.msc". This will allow you to see the status, version and manufacturer information of the TPM that is installed on your motherboard.
If you are using Windows 10, your computer may not have a TPM device installed, or if it is a computer assembled by you and you know that your computer has a TPM microcontroller, it might simply not be enabled.
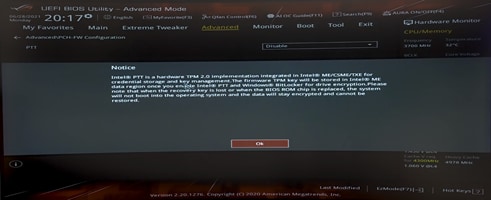
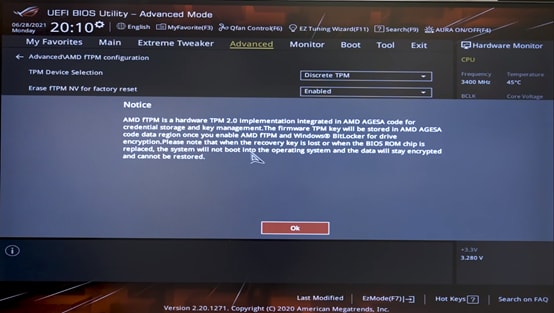
To enable it you must access the UEFI / BIOS of your computer and enable it. This is usually accomplished by pressing "DEL" or "F2." The process may vary slightly from computer to computer because there are many motherboard models and each of them has specialized firmware. Check your motherboard manufacturer's user manual or website for details on how to access its UEFI / BIOS utility.
Intel
If your computer uses an Intel processor, in the UEFI / BIOS you should be able to find a section in the “Advanced” category called “Advanced \ PCH-FW Configuration”. In it you will find the option to enable the "Intel PTT" driver.
AMD
If your computer uses an AMD processor, in the UEFI / BIOS you should be able to find a section in the “Advanced” category called “Advanced \ AMD fTPM Configuration”. In it you will find the option to enable the "AMD fTPM" driver.
Feature 2: Virtualization-Based Security (VBS) and HVCI
To understand virtualization-based security, it is imperative to understand what virtualization is. Virtualization basically consists of replicating conditions and characteristics through software. This means that there are hundreds of things that can be replicated virtually, including operating systems and hardware resources.
Virtualization
Virtualization is very much like imagination in concept. You can use a computer and use virtualization software to create virtual computers. In theory, it is possible to create as many virtual computers as you want, but you must bear in mind that the main limitation is the resources available to the computer that performs the virtualization. This procedure can be used for many purposes, one of the most common is to carry out tests or processes that require a controlled environment.
For example: To determine how a software would perform in multiple hypothetical cases, with different operating systems, configurations, with a higher or lower power processor, more or less virtual memory, etc.
VBS
VBS (Virtualization-Based Security) uses hardware virtualization features to create and isolate a security section in memory from the rest of the operating system. Windows can use this section to host all kinds of security tools, making them practically inaccessible and immune to vulnerabilities that can be found in the operating system and preventing the use of malicious exploits that try to disable Windows security systems.
HVCI
Hypervisor-Enforced Code Integrity (HVCI) is a security protocol that relies on VBS to significantly strengthen the application of security standards, corroborating the integrity of the code before being executed and preventing that unverified drivers or system files are uploaded.
With Windows 11 it is likely that this feature is configured at the factory but in case you use Windows 10, or need to activate it on your own, follow the steps below.
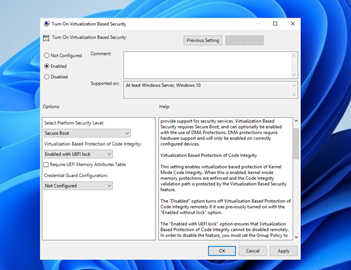
Open to the Group Policy Editor tool. You can do this by pressing “Win+R” and then typing “gpedit.msc”.
Go to this route: Computer Configuration / Administrative Templates / System / Device Guard.
Double-click on “Turn on Virtualization Based Security”.
Click on “Enabled” button and under “Virtualization Based Protection of Code Integrity”, select “Enabled with UEFI lock” to ensure HVCI cannot be disabled remotely or select “Enabled without UEFI lock”, then just click on “Ok“.
Feature 3: Microsoft Defender Application Guard (MDAG)
The use of MDAG is very common in companies and work environments because, according to the data collected by the most important cyber security organizations in the US, they indicate that the main cause of a company's data being compromised is due to negligence of workers when surfing the internet. This security feature keeps the user and the data of their work team safe from all types of cyber-attacks.
Microsoft Defender Application Guard (MDAG) is a security feature included since Windows 10. This feature is designed to virtualize and temporarily isolate Microsoft office tools and the Microsoft Edge browser, as well as their use of network resources, keeping isolated and secure to the operating system and the network to which it is connected in case the user accesses unsafe websites or tries to open files from the Microsoft office suite (Word, PowerPoint, Excel, etc.) that are not trusted.
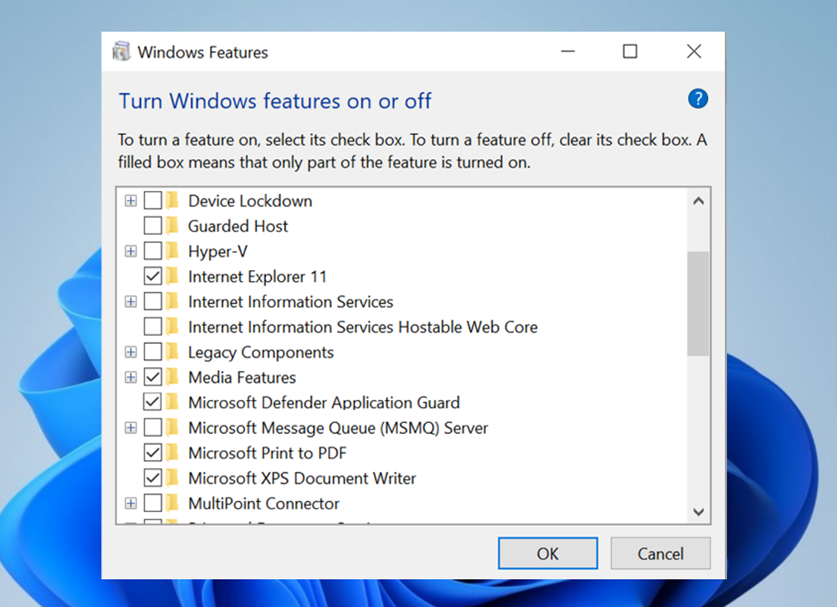
MDAG is disabled by default in Windows 10 but it can be easily enabled. You just need to go to the Windows menu, type “Windows Features” and click on the icon with the same name. Next, a window will appear where you can easily activate or deactivate Windows features by simply checking its corresponding box.
Closing Words
Now you know the three most important security features that Windows 11 will bring with it. If you already have a Windows 11 installation, you will not need to configure or activate any of them. However, if you are using Windows 10 and want to upgrade to Windows 11, you can try enabling these features to familiarize yourself with the changes to come. Also, keep in mind that, for now, having a TPM 2.0 microcontroller is a requirement to install Windows 11, so it is advisable that you confirm that your computer has one before trying to update.
Wondershare PDFelement
Simplify how people interact and communicate with PDF documents using intuitive and powerful PDF tools.