Today, millions of people perform the functions of their positions working from home. For some, this is a very positive change as it allows them to spend more time close to family or simply at home, while for others, remote work seems inefficient and unsafe. To understand the latter, it is necessary to know the origin of the remote work arrangement. What has changed, and why is remote work so important today?
In this article
Part 1. The Importance of Securing Documents for Remote Work
When access to technology began to be democratized, many companies started to consider remote work a viable option since it no longer represented a high management cost. However, there were still problems to be solved. Remote working was believed to decrease social interaction between workers, reduce workers' morale, make collaboration difficult, and put company information at risk.
It is currently necessary to comply with specific social distancing measures, so companies have accelerated solving social interaction and cooperation problems. Now a day, companies invest a lot of money and effort in improving their remote work management and training their staff. However, one of the main concerns of companies and workers is to prevent the information they work with from being compromised.
The data breach is not a game. According to data provided by some of the most prominent cybersecurity companies in the US, the average cost of a data breach to companies worldwide is $ 3.86 million. Fortunately, today, there are file management tools that rely on cryptography to keep information protected.
Wondershare PDFelement
Simplify how people interact and communicate with PDF documents using intuitive and powerful PDF tools.
Part 2. How to Secure Client Documents While Working Remotely
When working remotely, you need to send and receive information over the internet. The problem with the internet for remote workers is that they do not have the same security infrastructure as the company's offices. So, each remote worker must take precautionary measures to prevent company information from falling into the wrong hands.
Malware attacks: Malware is essentially software usually intentionally uploaded to the network to be downloaded through hoaxes. This software can steal all kinds of information in the background without the user being aware of it. In addition, you must know that malware based on cryptovirology is specially designed to block access to it unless a ransom is paid. These are known as Ransomware, and according to data provided by cybersecurity companies in the US, a new organization will fall victim to Ransomware every 11 seconds by 2022.
Phishing: Phishing consists of social engineering techniques that tricking people into voluntarily offering personal information such as passwords for access to social networks, cloud storage services or business software. In general, these types of tricks are carried out through email, forums and social networks. Note that 30% of phishing messages get opened by targeted users, and 12% of those users click on the malicious attachment or link.
Method 1. Redact information
Although it's hard to believe, you should start taking security measures long before sharing your files. From the moment you begin to write the information, you should follow a series of tips.
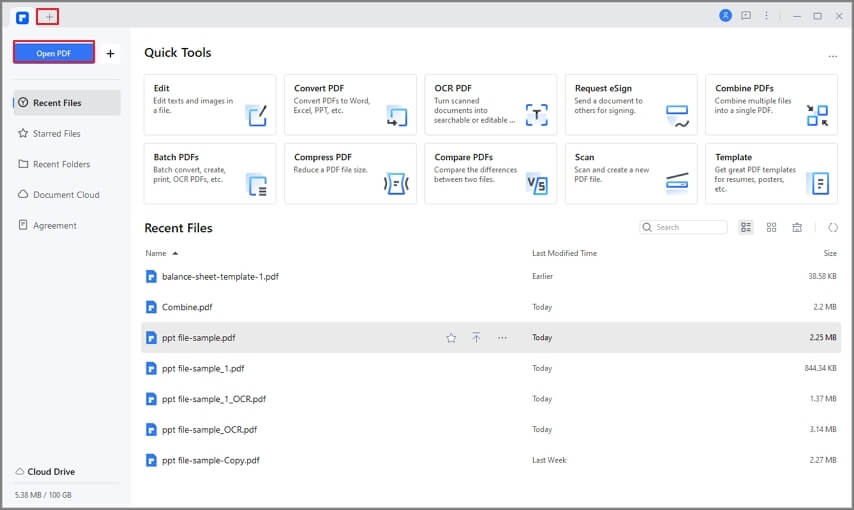
Use PDF technology
PDF technology is renowned for ensuring that documents can be viewed accurately from any device. However, this is not the only advantage that this PDF technology offers. There are PDF document management programs such as PDFelement that allow the use of cryptographic security systems. With these, you can draft your documents with complete confidence that they will never be decrypted even if they get into the wrong hands.
Stay updated
It is usual for software to have vulnerabilities. It is not until someone discovers and reports them that the software companies can develop updates to correct these problems. Ensure that the operating system and software you work on are updated, as these can prevent the information you work with from being compromised.
Work only with secure pages
If you need to surf the internet at any time, make sure you only visit sites with an SSL certificate, as these ensure that data traffic is encrypted. All you have to do is make sure that the URL web domains you visit are prefixed with HTTPS and not HTTP.
Protect your browsing with a VPN
A VPN (Virtual Private Network) connects to a network that acts as a filter between your computer and your network service provider. In short, you use an intermediary to protect your identity, location and at the same time take advantage of a network specially configured to be secured. Your information will travel encrypted so, even if a cybercriminal manages to intercept it, it would be indecipherable for him.
PDFelement-Powerful and Simple PDF Editor
Get started with the easiest way to manage PDFs with PDFelement!
Method 2. Encrypt documents
Data encryption consists of treating a file as a set of bits, taking a small segment of these bits and a password chosen by the user to use as a reference in an algorithm that manages to represent the document's current state. The rest of the bits are disordered to generate chaos, and the small segment of bits is used, as well as the password that the user designated to solve the algorithm that manages to put all the bits back in their original place.
Depending on the number of values used to generate the cryptographic key, it can be considered more or less secure. However, it is essential to note that using a segment of only 128 bits. It could take criminals thousands of years to solve the algorithm through trial and error. (Brute force attack). Fortunately, with tools like PDFelement, you can protect your documents with this technology.
All you have to do is open your document with PDFelement, click on the "Protect" section, check the "Open Password" box and enter a password, select an encryption level and click "Save."
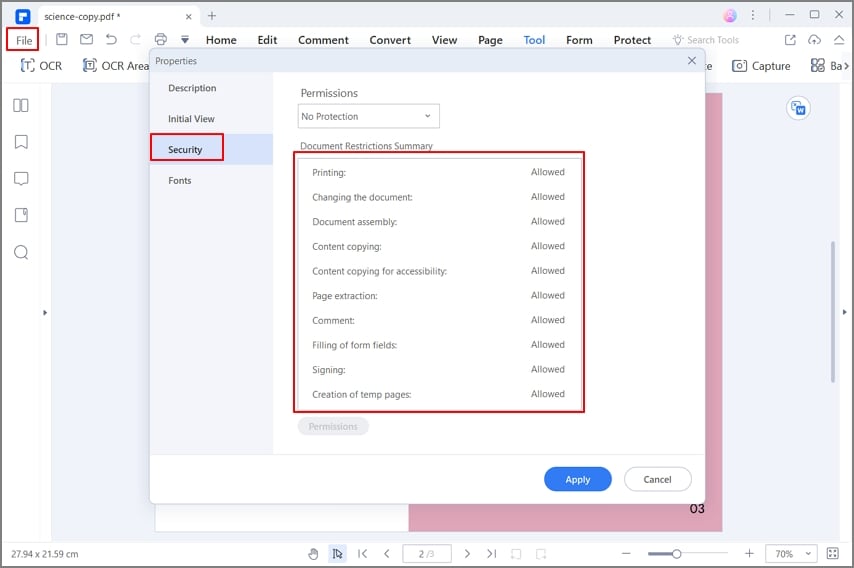
Method 3. Implement a document access
Permission restriction is not new. Windows allows you to assign read and write permissions. However, when working with text documents, you are expected to want certain people to read and make changes to a document. Using PDFelement, you can quickly fix this problem. This software allows you to assign specific permissions so that certain people can read and modify the document.
If this is your case, you can check the "Permission Password" box to establish specific permissions, and when finished, select an encryption level and click "Save."
Closing Words
Remote work is currently a necessity. Many companies are doing their best to keep up with work while ensuring information security and their workers through remote work. Many cybercriminal organizations are trying to take advantage of this, and that is why, today more than ever, we need to take precautions concerning information management. PDFelement is a straightforward tool to use, and with it, you can guarantee that the information you work with will be safe at all times.
